Note: Google Drive links may not work or might be expired. You can find the scripts here
Tutorial no 8
L2_firewall
Firewall is security approach in networking. Design aspect of firewall are according need of administrator. Here we are going to implement layer2 MAC based firewall which forwards only listed MAC host’s packets and rejects other’s traffic. It is somewhat similar to NOX’s pyswitch in that it installs. POX does not contain firewall scripts. You can copy code or can download from here.
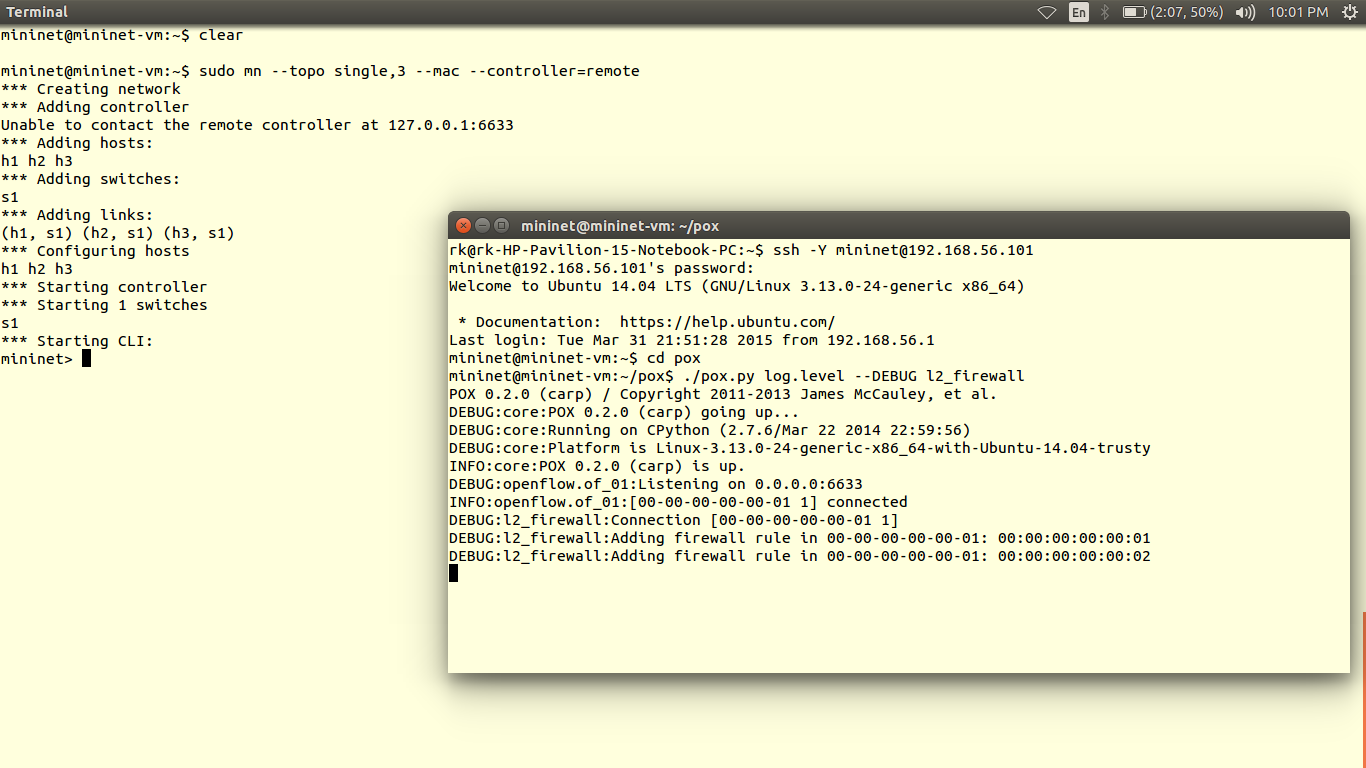
1) To save code of l2_firewall script, ssh into mininet and go to pox/ext. Open nano Copy and paste the code. Use key ‘CTRL+O’ to save code and ‘CTRL+X’ to exit nano editor. I have saved code with name l2_firewall.py
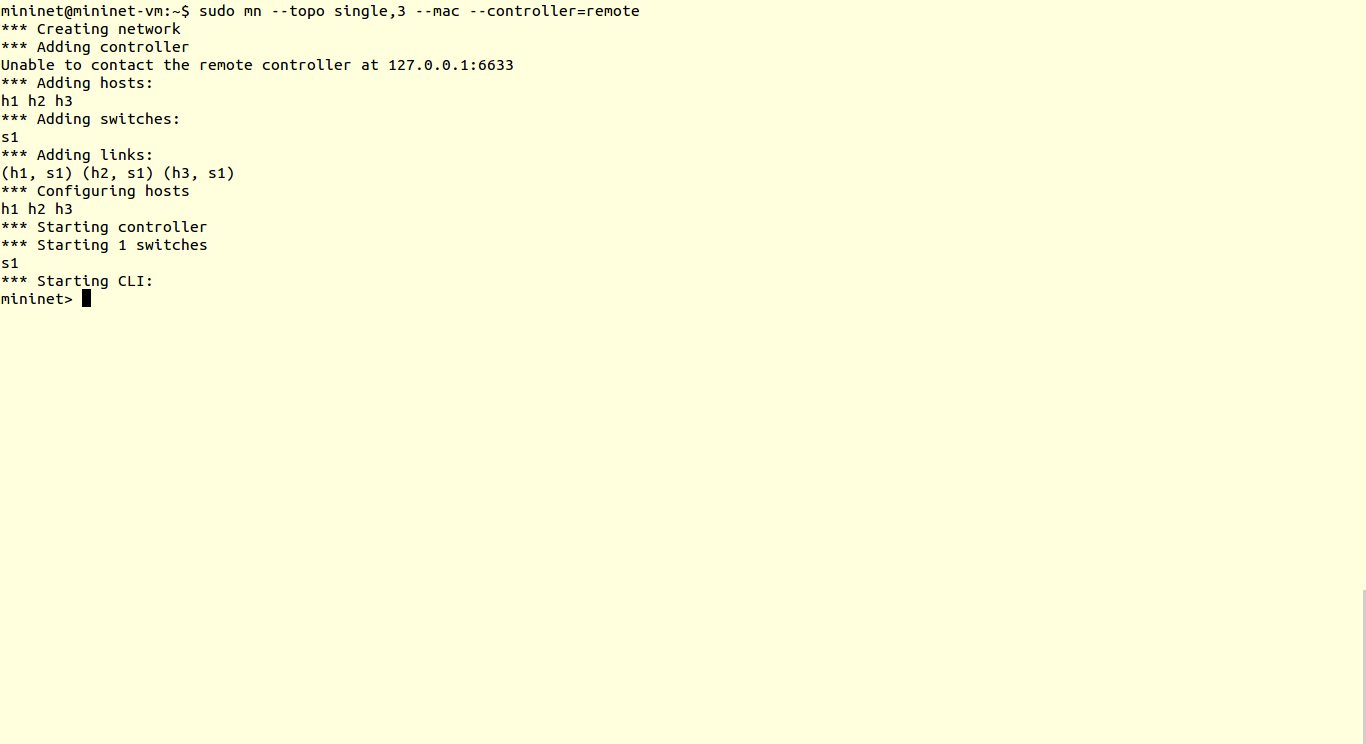
2) Now we will create topology with one controller one switch and 3 hosts.
We are going to forward packets of hosts with MAC 00:00:00:00:00:1, 00:00:00:00:00:2 and packets from other hosts (host3) are dropped.
Now let’s run firewall scripts which we have saved in pox/ext .
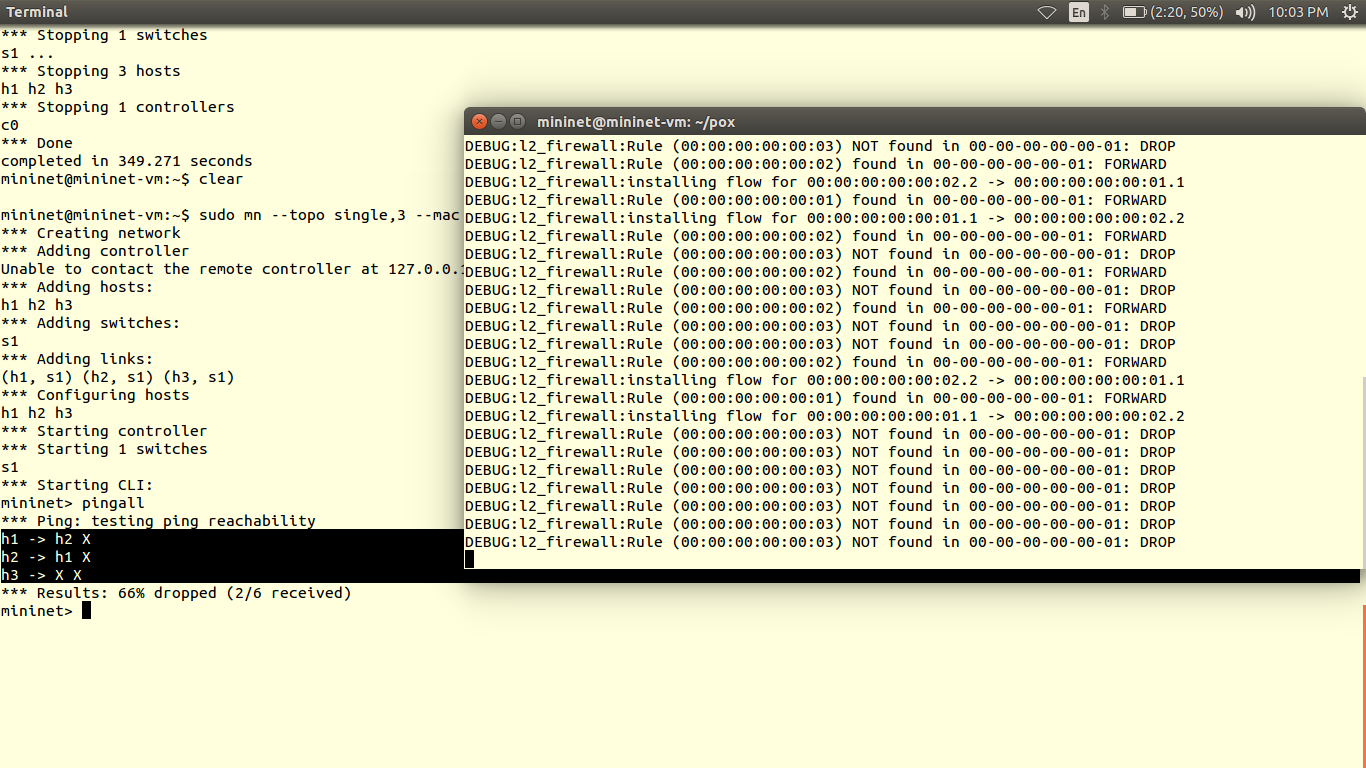
3) We can check results using pingall You can observe there is connectivity between host1 (00:00:00:00:00:1) and host2 (00:00:00:00:00:2) since we have allowed forwarding rule for the firewall script. Similarly we can change the MAC in the script and forward traffic or set layer2 firewall rule based on MAC address of devices.
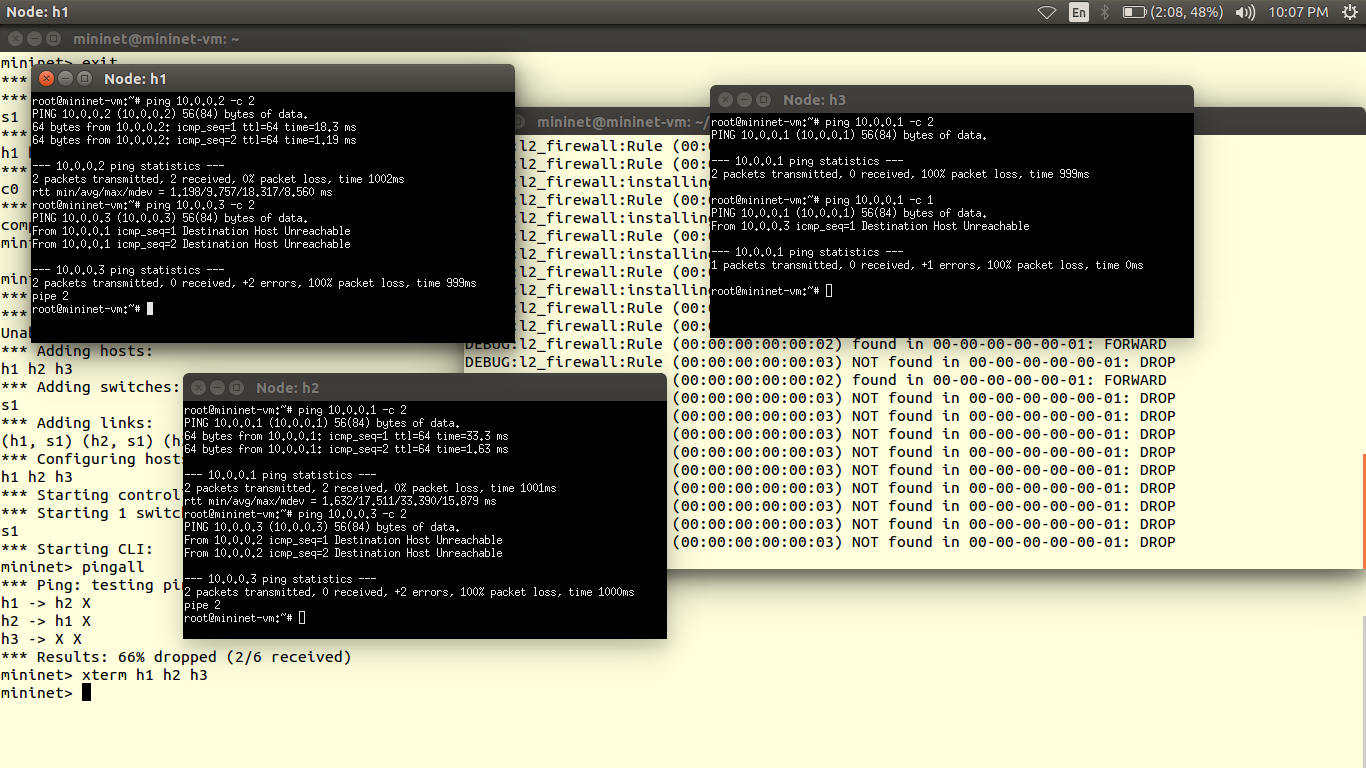
4) You can also check ping result from indidual hosts using XTERM.
Credits: Firewall script from Nick Feamster’s coursera SDN course